PKI Consortium blog
Posts by tag Policy
Secure Your Website with HSTS
October 8, 2014 by
Bruce Morton
(Entrust)
Attack
Chrome
Encryption
Firefox
Google
HSTS
Policy
SSL/TLS
Is your website secure? One thing to consider is securing your website with HTTP Strict Transport Security (HSTS).
Implementation of HSTS is an extension of the Always-On SSL policy. For each website you want to protect with HSTS, you must first deploy an SSL/TLS certificate (if you haven’t already), and configure that website to be accessible only via HTTPS, not via HTTP. Then you convey to HSTS-enabled browsers that your site is only available with HTTPS, by sending the HSTS header value. Supporting browsers will automatically change any HTTP query for your website into an HTTPS query. If there is no HTTPS version available, then the browser will provide a trust dialogue to the user.
Google Plans to Deprecate SHA-1 Certificates – Updated
September 24, 2014 by
CA Security Council
Announcement
Attack
CASC
Chrome
Code Signing
Google
Microsoft
Policy
SHA1
SSL/TLS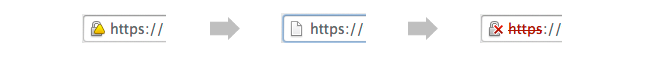
UPDATED September 23, 2014: The following blog post has been updated with action taken in recent weeks, as well as to reflect helpful user comments left on our August 28 blog post on this topic.
On August 19, Google announced a new policy that accelerates the deprecation of SHA-1 certificates, potentially causing websites using SHA-1 certificates to display warnings in the near future. While keeping with an earlier Microsoft announcement to accept SHA-1 certificates with an expiration date before Jan. 1, 2017, the Google policy will provide new “untrusted” warnings in regards to such certificates as early as this November.
Google Plans to Deprecate SHA-1 Certificates
August 28, 2014 by
CA Security Council
Attack
CASC
Chrome
Code Signing
Google
Microsoft
Policy
SSL/TLS
On August 19, Google announced a new policy that accelerates the deprecation of SHA-1 certificates, potentially causing websites using SHA-1 certificates to display warnings in the near future. With the change, Chrome 39 will show a warning for sites that have a SHA-1 certificate expiring in 2016 and require a click through warning for sites with a SHA-1 certificate expiring in 2017 or later. This proposal is scheduled for Chrome 39, which could be released as early as 12 weeks from now.
Who Sets the Rules Governing Certification Authorities?
August 19, 2014 by
Kirk Hall
(Entrust)
CA/Browser Forum
Code Signing
DV
Encryption
ETSI
EV
Google
Hash Function
Identity
IETF
Microsoft
Mozilla
OCSP
Policy
Revocation
Root Program
SSL/TLS
WebTrust
Every time something positive is published about SSL and encryption,such as Google’s recent decision making use of https encryption a favorable rating factor for a website, or negative, such as the Heartbleed issue – bloggers and others always post questions about public Certification Authorities (CAs), including general questions on who sets the rules that govern CAs. Some bloggers seem to assume there are no rules or standards, and that CAs can operate without any requirements or limitations at all — that’s incorrect.
In the Wake of Unauthorized Certificate Issuance by the Indian CA NIC, can Government CAs Still be Considered “Trusted Third Parties”?
July 24, 2014 by
Ben Wilson
CA/Browser Forum
CAA
CASC
Chrome
ETSI
Firefox
Google
Microsoft
Mis-issued
Mozilla
OCSP
PKI
Policy
Revocation
SSL/TLS
Trust List
WebTrust
Short answer: Government CAs can still be considered “trusted third parties,” provided that they follow the rules applicable to commercial CAs.
Introduction
On July 8 Google announced that it had discovered several unauthorized Google certificates issued by the National Informatics Centre of India. It noted that the Indian government CA’s certificates were in the Microsoft Root Store and used by programs on the Windows platform. The Firefox browser on Windows uses its own root store and didn’t have these CA certificates. Other platforms, such as Chrome OS, Android, iOS, and OS X, were not affected. See http://googleonlinesecurity.blogspot.com/2014/07/maintaining-digital-certificate-security.html
Always-On SSL, Part II
February 5, 2014 by
Ben Wilson
Encryption
Firefox
Mixed Content
Policy
Qualified
SSL/TLS
The SSL/TLS protocol has more to offer than just providing you with transmission encryption. Its main benefit is that it provides a way for third parties to authenticate connections to your website over the Internet. A user who can connect to your site and retrieve information via SSL/TLS will have greater assurance and trust that information came from you. The point of Always-On SSL is that once a user is able to create an authenticated connection to your point of presence via https, then he or she should not be bounced back outside of that zone of protection. When content is communicated via HTTPS, it is because you expect to provide a level of security — and your users come to expect them as well. Once you welcome a visitor, it makes no sense to have them go back outside in order to knock. This is just one of several illustrations I’d like to present where heightened protection of a visitor should be maintained, and hopefully these examples will illustrate why Always-On SSL is the preferred method for providing web visit security.
Intermediate CA Certificates and Their Potential For Misuse For Man-In-The-Middle Attacks
January 9, 2014 by
Robin Alden
(Sectigo)
Attack
Firefox
Google
MITM
Policy
Root Program
SSL/TLS
Vulnerability
We have seen recently that Google detected that publicly trusted TLS/(SSL) certificates had been created for Google domains without having been requested by Google themselves.
The existence of such certificates might usually be taken as an indication of misissuance by the issuing CA (i.e. a failure or mistake by the CA which allowed the issuance of an end-entity certificate otherwise than in accordance with their policy) or as an indication of compromise of the issuing CA.
2014 – Looking Back, Moving Forward
January 6, 2014 by
Bruce Morton
(Entrust)
Attack
BEAST
CA/Browser Forum
CAA
Code Signing
ECC
Encryption
Forward Secrecy
HSTS
ICANN
IETF
Microsoft
MITM
Mozilla
PKI
Policy
RC4
RSA
SHA1
SSL/TLS
TLS 1.2
Looking Back at 2013
Protocol Attacks
The year started with a couple of SSL/TLS protocol attacks: Lucky Thirteen and RC4 attack. Lucky Thirteen allows the decryption of sensitive information, such as passwords and cookies, when using the CBC-mode cipher suite. Lucky Thirteen can be mitigated by implementing software patches or preferring the cipher suite RC4.
ICANN’s Accelerated gTLD Delegation Process and How This Impacts Your Organization
December 18, 2013 by
Jeremy Rowley
Announcement
CA/Browser Forum
CASC
ICANN
MITM
Mozilla
PKI
Policy
Qualified
Revocation
SSL/TLS
Vulnerability
After the CASC’s previous letter addressing ICANN’s proposal to delegate nearly 2000 new gTLDs for use on the public Internet, ICANN identified and initiated an extensive study on two significant security issues. Now, based on the conclusions of the studies, ICANN is moving forward quickly with the delegation process, delegating more than 30 in the last two months alone. With ICANN ramping up the delegation process, nearly all 2000 will be delegated under the new rules, with only .corp and .home reserved as high risk gTLDs. This post serves as an advisory for interested network administrator on how the newest ICANN decisions may affect their networks and certificates.
SHA-1 Deprecation, On to SHA-2
December 16, 2013 by
Bruce Morton
(Entrust)
Code Signing
Microsoft
PKI
Policy
SHA1
SSL/TLS
We have previously reviewed implementation of SHA-2, but with Bruce Schneier stating the need to migrate away from SHA-1 and the SHA-1 deprecation policy from Microsoft, the industry must make more progress in 2014.
Web server administrators will have to make plans to move from SSL and code signing certificates signed with the SHA-1 hashing algorithm to certificates signed with SHA-2. This is the result of the new Microsoft Root Certificate Policy where Microsoft deprecates SHA-1 and imposes the following requirements:










































































