PKI Consortium blog
Posts by tag Microsoft
Google Plans to Deprecate SHA-1 Certificates – Updated
September 24, 2014 by
CA Security Council
Announcement
Attack
CASC
Chrome
Code Signing
Google
Microsoft
Policy
SHA1
SSL/TLS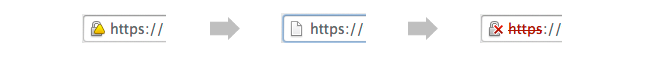
UPDATED September 23, 2014: The following blog post has been updated with action taken in recent weeks, as well as to reflect helpful user comments left on our August 28 blog post on this topic.
On August 19, Google announced a new policy that accelerates the deprecation of SHA-1 certificates, potentially causing websites using SHA-1 certificates to display warnings in the near future. While keeping with an earlier Microsoft announcement to accept SHA-1 certificates with an expiration date before Jan. 1, 2017, the Google policy will provide new “untrusted” warnings in regards to such certificates as early as this November.
Google Plans to Deprecate SHA-1 Certificates
August 28, 2014 by
CA Security Council
Attack
CASC
Chrome
Code Signing
Google
Microsoft
Policy
SSL/TLS
On August 19, Google announced a new policy that accelerates the deprecation of SHA-1 certificates, potentially causing websites using SHA-1 certificates to display warnings in the near future. With the change, Chrome 39 will show a warning for sites that have a SHA-1 certificate expiring in 2016 and require a click through warning for sites with a SHA-1 certificate expiring in 2017 or later. This proposal is scheduled for Chrome 39, which could be released as early as 12 weeks from now.
Who Sets the Rules Governing Certification Authorities?
August 19, 2014 by
Kirk Hall
(Entrust)
CA/Browser Forum
Code Signing
DV
Encryption
ETSI
EV
Google
Hash Function
Identity
IETF
Microsoft
Mozilla
OCSP
Policy
Revocation
Root Program
SSL/TLS
WebTrust
Every time something positive is published about SSL and encryption,such as Google’s recent decision making use of https encryption a favorable rating factor for a website, or negative, such as the Heartbleed issue – bloggers and others always post questions about public Certification Authorities (CAs), including general questions on who sets the rules that govern CAs. Some bloggers seem to assume there are no rules or standards, and that CAs can operate without any requirements or limitations at all — that’s incorrect.
In the Wake of Unauthorized Certificate Issuance by the Indian CA NIC, can Government CAs Still be Considered “Trusted Third Parties”?
July 24, 2014 by
Ben Wilson
CA/Browser Forum
CAA
CASC
Chrome
ETSI
Firefox
Google
Microsoft
Mis-issued
Mozilla
OCSP
PKI
Policy
Revocation
SSL/TLS
Trust List
WebTrust
Short answer: Government CAs can still be considered “trusted third parties,” provided that they follow the rules applicable to commercial CAs.
Introduction
On July 8 Google announced that it had discovered several unauthorized Google certificates issued by the National Informatics Centre of India. It noted that the Indian government CA’s certificates were in the Microsoft Root Store and used by programs on the Windows platform. The Firefox browser on Windows uses its own root store and didn’t have these CA certificates. Other platforms, such as Chrome OS, Android, iOS, and OS X, were not affected. See http://googleonlinesecurity.blogspot.com/2014/07/maintaining-digital-certificate-security.html
What To Do When You Rely on Internal Names in TLS/SSL Certificates
July 18, 2014 by
Wayne Thayer
Attack
CA/Browser Forum
Firefox
IANA
ICANN
Microsoft
MITM
Qualified
SSL/TLS
A deadline set by the CA/Browser Forum for the use of Internal Names is quickly approaching, and many system administrators need to understand how best to adapt to this change. At the same time, hundreds of new top-level domains are being launched, which redefines what constitutes an Internal Name. In this post we’ll explain what the changes are, why they’re being made, and how you can update your systems in response to the problem.
Certificate Reputation
March 28, 2014 by
Bruce Morton
(Entrust)
Microsoft
MITM
OCSP
PKI
SSL/TLS
One of the advantages of having multiple certification authorities (CAs) from which to choose an SSL certificate is that customers have flexibility to choose a CA that meets their specific needs, or even use a number of CAs for redundancy or to have access to a broader toolset. The disadvantage for end users, however, is that they often may not know if a particular CA was authorized to issue the certificate, and there could be a chance that the certificate was fraudulently obtained.
CA Security Council Members Presentation at RSA 2014 Conference: New Ideas on CAA, CT, and Public Key Pinning for a Safer Internet
March 17, 2014 by
Kirk Hall
(Entrust)
Attack
CAA
CASC
Chrome
EV
Google
IETF
Microsoft
Mis-issued
OCSP
Revocation
RSA
SSL/TLS
Vulnerability
CA Security Council (CASC) members Trend Micro, Go Daddy, and Symantec participated in a discussion panel at the 2014 RSA Conference in San Francisco on February 24 entitled “New Ideas on CAA, CT, and Public Key Pinning for a Safer Internet.” Panel members included Kirk Hall of Trend Micro (Moderator), Wayne Thayer of GoDaddy (Panelist), and Rick Andrews of Symantec (Panelist).
Introduction to the Topic
Hall began by introducing the topic – all three alternative technologies (Certificate Transparency or CT, Certificate Authority Authorization or CAA, and Certificate Pinning) are intended to make the internet safer by dealing with mis-issued digital certificates, including so-called “rogue” certs like those obtained by a hacker from the now-defunct Diginotar Certification Authority (CA). Mis-issued certs generally present the greatest potential danger when they are for the most popular fraud target domains, such as mail.google.com, login.yahoo.com, login.live.com, etc.
Pros and Cons of Single-Domain, Multi-Domain, and Wildcard Certificates
February 26, 2014 by
Wayne Thayer
Microsoft
SSL/TLS
We have previously written about the different types of SSL certificates, but in that article we focused on validation levels. A recent post on LinkedIn highlighted the fact that there is another dimension that we haven’t yet explored.
SSL certificates come in three basic packages: “single-domain” certificates that can only be used on one specific website, “multi-domain” certificates that can be used on more than one website, and “wildcard” certificates that can be used on any website within a specific domain name. Multi-domain certificates are often called “unified communications” or “UC” certificates. This is a reference to one common use of these certificates, which is to secure Microsoft messaging products such as Exchange and Lync. The table below shows examples of the number and types of websites that each of these packages can protect:
CA Day in Berlin
January 24, 2014 by
Dean Coclin
eIDAS
ETSI
EV
Microsoft
PKI
Qualified
Root Program
RSA
SSL/TLS
TSP
“CA Day” (also known as CA Conformity Assessment) was hosted by the German company TuVIT in Berlin on January 16, 2014. In attendance were approximately 100 people from mostly European CAs. Under the European regulatory framework, CAs are included in a group referred to as “Trust Service Providers” or “TSPs.” CASC members in attendance at CA Day were Symantec, Digicert and Comodo. The dominant theme for this CA Day was the draft Regulation on Electronic identification and trust services for electronic transactions in the internal market (eIDAS) and upcoming changes in EU regulations for Qualified Certificates, which was briefed by Gerard Galler from the European Commission and discussed in greater detail by several European TSPs. eIDAS includes a proposal for EU Qualified Website certificates (i.e. SSL) using the Extended Validation certificate as a regulatory baseline. Under proposed Article 37, qualified website certificates could only be issued by EU Qualified CAs which have been audited according to ETSI (European Telecommunications Standards Institute) standards by an approved auditor. If promulgated by the European Parliament, the Commission would be empowered to give EU Qualified EV SSL certificates the “backing” of EU law.
Always-On SSL, Part I
January 16, 2014 by
Rick Andrews
Encryption
Google
Identity
Microsoft
Mixed Content
OpenSSL
SSL/TLS
There is no doubt that content owners and publishers have a duty to encourage trust and the confidence during internet usage by adopting security best practices. If a customer believes that their data and identity are safe and protected, they are more inclined to continue their online transactions. Industry best practices for website protection should be vendor-neutral, easy to implement, and globally accessible. Websites should take all the reasonable steps possible to adopt best practices in secure design and implementation, and this includes using Always-On SSL across the entire website.













































































