PKI Consortium blog
Posts by tag Google
A Follow-up on POODLE and SSL 3.0
November 21, 2014 by
Bruce Morton
(Entrust)
Attack
Encryption
Google
IETF
Mozilla
OpenSSL
SSL 3.0
SSL/TLS
TLS 1.0
TLS 1.1
TLS 1.3
Vulnerability
In October 2014, Google announced POODLE, an SSL 3.0 protocol attack.
To bring you up to speed, the SSL/TLS protocol is the most important and popular security protocol on the Internet. The Secure Sockets Layer (SSL) protocol was developed by Netscape. They quickly moved from SSL 1.0 to 2.0 and finalized with SSL 3.0 in 1996.
This protocol was then picked up by the IETF, who released it under the name of Transport Layer Security (TLS). The IETF released TLS 1.0, 1.1 and 1.2. They are currently working on TLS 1.3.
Extra Trips are for Frequent Flyers, Not SSL/TLS Performance
October 30, 2014 by
Wayne Thayer
Firefox
Forward Secrecy
Google
HSTS
OCSP
Revocation
RSA
SSL/TLS
TLS is quickly becoming a de facto requirement for every website due to increased concerns about spying and Google’s recent move to use HTTPS as a factor in search engine ranking. In a recent article we explained how HSTS helps website operators to ensure that their site is always using TLS, but now we want to ensure that your performance isn’t sacrificed in the name of enhanced security. While the myth that TLS slows down a website has been debunked, some basic settings can make a site using TLS even faster.
Secure Your Website with HSTS
October 8, 2014 by
Bruce Morton
(Entrust)
Attack
Chrome
Encryption
Firefox
Google
HSTS
Policy
SSL/TLS
Is your website secure? One thing to consider is securing your website with HTTP Strict Transport Security (HSTS).
Implementation of HSTS is an extension of the Always-On SSL policy. For each website you want to protect with HSTS, you must first deploy an SSL/TLS certificate (if you haven’t already), and configure that website to be accessible only via HTTPS, not via HTTP. Then you convey to HSTS-enabled browsers that your site is only available with HTTPS, by sending the HSTS header value. Supporting browsers will automatically change any HTTP query for your website into an HTTPS query. If there is no HTTPS version available, then the browser will provide a trust dialogue to the user.
Google Plans to Deprecate SHA-1 Certificates – Updated
September 24, 2014 by
CA Security Council
Announcement
Attack
CASC
Chrome
Code Signing
Google
Microsoft
Policy
SHA1
SSL/TLS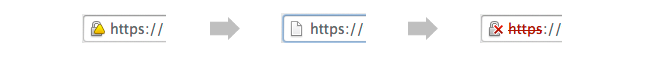
UPDATED September 23, 2014: The following blog post has been updated with action taken in recent weeks, as well as to reflect helpful user comments left on our August 28 blog post on this topic.
On August 19, Google announced a new policy that accelerates the deprecation of SHA-1 certificates, potentially causing websites using SHA-1 certificates to display warnings in the near future. While keeping with an earlier Microsoft announcement to accept SHA-1 certificates with an expiration date before Jan. 1, 2017, the Google policy will provide new “untrusted” warnings in regards to such certificates as early as this November.
Google Plans to Deprecate SHA-1 Certificates
August 28, 2014 by
CA Security Council
Attack
CASC
Chrome
Code Signing
Google
Microsoft
Policy
SSL/TLS
On August 19, Google announced a new policy that accelerates the deprecation of SHA-1 certificates, potentially causing websites using SHA-1 certificates to display warnings in the near future. With the change, Chrome 39 will show a warning for sites that have a SHA-1 certificate expiring in 2016 and require a click through warning for sites with a SHA-1 certificate expiring in 2017 or later. This proposal is scheduled for Chrome 39, which could be released as early as 12 weeks from now.
Google to Give Priority Ranking to SSL Enabled Sites
August 21, 2014 by
Chris Bailey
(AppViewX)
Chris Bailey
(Entrust)
Announcement
Google
SSL/TLS
Google’s announcement that it will give priority ranking to SSL enabled sites is a key milestone for increased use of SSL on the Internet.
Google announced a change to its ranking algorithm to include use of SSL on the site as a “very lightweight [positive] signal”. Although, this might not have an immediate impact to website owners/operators that are not currently using SSL, this is still an important signal indicating everyone should be prepared to encrypt all their websites if they want to remain relevant.
Who Sets the Rules Governing Certification Authorities?
August 19, 2014 by
Kirk Hall
(Entrust)
CA/Browser Forum
Code Signing
DV
Encryption
ETSI
EV
Google
Hash Function
Identity
IETF
Microsoft
Mozilla
OCSP
Policy
Revocation
Root Program
SSL/TLS
WebTrust
Every time something positive is published about SSL and encryption,such as Google’s recent decision making use of https encryption a favorable rating factor for a website, or negative, such as the Heartbleed issue – bloggers and others always post questions about public Certification Authorities (CAs), including general questions on who sets the rules that govern CAs. Some bloggers seem to assume there are no rules or standards, and that CAs can operate without any requirements or limitations at all — that’s incorrect.
In the Wake of Unauthorized Certificate Issuance by the Indian CA NIC, can Government CAs Still be Considered “Trusted Third Parties”?
July 24, 2014 by
Ben Wilson
CA/Browser Forum
CAA
CASC
Chrome
ETSI
Firefox
Google
Microsoft
Mis-issued
Mozilla
OCSP
PKI
Policy
Revocation
SSL/TLS
Trust List
WebTrust
Short answer: Government CAs can still be considered “trusted third parties,” provided that they follow the rules applicable to commercial CAs.
Introduction
On July 8 Google announced that it had discovered several unauthorized Google certificates issued by the National Informatics Centre of India. It noted that the Indian government CA’s certificates were in the Microsoft Root Store and used by programs on the Windows platform. The Firefox browser on Windows uses its own root store and didn’t have these CA certificates. Other platforms, such as Chrome OS, Android, iOS, and OS X, were not affected. See http://googleonlinesecurity.blogspot.com/2014/07/maintaining-digital-certificate-security.html
CASC Heartbleed Response
May 8, 2014 by
CA Security Council
CASC
Chrome
CRL
Google
Malware
OCSP
Revocation
SSL/TLS
The recent Heartbleed issue has reawakened interest in SSL certificate revocation (see Adam Langley’s blog, Larry Seltzer’s articles here and here, and Steve Gibson’s web pages)
Several years ago, the CA Browser Forum convened a special Revocation Working Group to explore issues and solutions. Leading CAs were actively involved in that group, and many of them invested in moving their OCSP responders to high-performance, high-availability Content Delivery Networks (CDNs) to respond to browser vendors’ requests for increased performance and reliability.
Revocation – A Cure For the Common Heartbleed
April 28, 2014 by
Jeremy Rowley
Attack
CASC
Chrome
CRL
Google
Identity
OCSP
Revocation
SSL/TLS
The Heartbleed bug spurred server administrators worldwide to work closely with Certification Authorities (CAs) in rekeying and reissuing potentially vulnerable SSL certificates. Part of this effort included revoking existing certificates used on vulnerable servers to ensure obtained private keys are not later used in a man-in-the-middle attack against the website. Unfortunately, in recent days, certain news reports and blogs addressing certificate revocation and checking for revoked certificates online have failed to discuss the benefits of revocation, instead focusing on the minority of circumstances where widely deployed revocation is not perfect. In the interest of providing balanced information to the public, we, as members of the CA community and as individuals generally interested in a high level of Internet security, would like to help clarify some of the issues confused by these reports and blogs.














































































