PKI Consortium blog
Posts by tag Forward Secrecy
The CA Security Council Looks Ahead to 2020 and Beyond
January 9, 2020 by
Patrick Nohe
(GlobalSign),
Doug Beattie
(GlobalSign)
Apple
CA/Browser Forum
Chrome
Edge
Encryption
EV
Firefox
Forward Secrecy
GDPR
Google
Identity
Microsoft
Mozilla
PKI
Policy
Qualified
SSL 3.0
SSL/TLS
TLS 1.0
TLS 1.1
TLS 1.2
TLS 1.3
Web PKI
A whirlwind of activity will cause dramatic shifts across the PKI world in the year ahead
Suffice it to say that 2019 was filled with challenges and contentiousness as Certificate Authorities and Browsers began to watch their shared visions diverge. The debate around Extended Validation continued as CAs pushed for a range of reforms and browsers pushed to strip its visual indicators. And a ballot to shorten maximum certificate validity periods exposed fault-lines at the CAB Forum.
2019 – Looking Back, Moving Forward
January 3, 2019 by
Bruce Morton
(Entrust)
Attack
CA/Browser Forum
Certificate Expiry
Chrome
Code Signing
DV
ECC
EV
Forward Secrecy
Identity
Mis-issued
Phishing
PKI
Policy
Qualified
Revocation
RSA
SSL/TLS
TLS 1.0
TLS 1.3
Vulnerability
Looking Back at 2018
2018 was an active year for SSL/TLS. We saw the SSL/TLS certificate validity period drop to 825-days and the mass deployment of Certificate Transparency (CT). TLS 1.3 protocol was finally completed and published; and Chrome status bar security indicators changing to remove “secure” and to concentrate on “not secure.” The CA/Browser Forum has been reformed, the London Protocol was announced and the nearly full distrust of Symantec SSL completed. Here are some details on some of the 2018 happenings in the SSL/TLS ecosystem.
TLS 1.3 Includes Improvements to Security and Performance
April 10, 2018 by
Tim Shirley
Forward Secrecy
IETF
SSL/TLS
TLS 1.2
TLS 1.3
Vulnerability
Last month saw the final adoption, after 4 years of work, of TLS version 1.3 by the Internet Engineering Task Force (IETF). This latest iteration of the protocol for secure communications on the internet boasts several noteworthy improvements to both security and performance:
Security
All cipher suites that do not provide forward secrecy have been eliminated from TLS 1.3. This is a very important security property, because without forward secrecy, if a server’s private key is compromised today, any previously-recorded conversations with that server dating back as long as the key was in use could be decrypted. While it is possible (and highly recommended) to configure a server with TLS 1.2 to prefer (or only support) cipher suites that provide forward secrecy, under TLS 1.3 these are the only option. Other cryptographic modernizations in TLS 1.3 include the elimination of DSA, custom DHE groups, and compression.
Stricter Standards for SSL Server Test Coming in 2017
December 13, 2016 by
Bruce Morton
(Entrust)
3DES
CASC
Forward Secrecy
RC4
SSL/TLS
TLS 1.3
Vulnerability
This is a good time to offer a reminder that the CASC has a great tool for secure server testing, the SSL Server Test. The tool grades your server installation and reviews the: certificate, protocol support, key exchange and cipher strength for security against standards and known vulnerabilities.
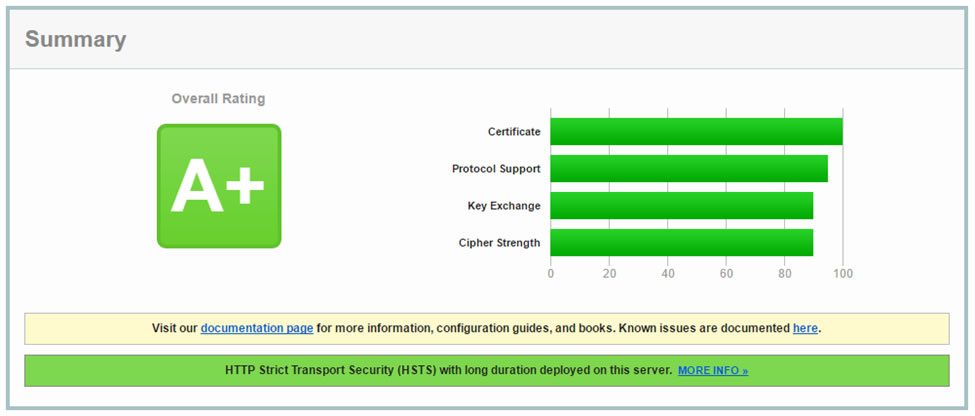
The grading tool also provides feedback on handshake simulations with various versions of browsers and operating systems. This lets the server administrator know which implementations are supported. The test also checks the server mitigation for known vulnerabilities such as: DROWN, BEAST, POODLE and Heartbleed.
HTTP/2 Is Speedy and Secure
April 20, 2015 by
Wayne Thayer
Announcement
Chrome
Firefox
Forward Secrecy
Google
HSTS
IETF
Microsoft
Mozilla
SSL/TLS
Vulnerability
Since we last wrote about SSL/TLS performance, there has been a lot of activity in the IETF HTTP Working Group, resulting in the February announcement that the next version of HTTP has been approved. This is big news because it means that major SSL/TLS performance improvements are on the way.
Background
When your browser connects to a website today, it most likely uses the HTTP/1.1 protocol that was defined in 1999 in RFC 2616. Over the past 15 years, HTTP/1.1 has served us well and many tweaks have been discovered to make the most of it. However, in that time the web has transformed into a platform for interactive content and applications. Today, browsers load much more data from many more sources to build the typical web page.
Is Your SSL Server Vulnerable to a FREAK Attack?
March 11, 2015 by
Bruce Morton
(Entrust)
Android
Attack
Encryption
Forward Secrecy
Microsoft
MITM
RSA
SSL/TLS
Vulnerability
FREAK is a new man-in-the-middle (MITM) vulnerability discovered by a group of cryptographers at INRIA, Microsoft Research and IMDEA. FREAK stands for “Factoring RSA-EXPORT Keys.”
The vulnerability dates back to the 1990s, when the US government banned selling crypto software overseas, unless it used export cipher suites which involved encryption keys no longer than 512-bits.
The issue is there are still some clients who let crypto be degraded from “strong RSA” to “export grade RSA”. These clients use OpenSSL, Apple’s Secure Transport and Windows Secure Channel. As such, users of Android mobiles, Apple Macs, iPhones and iPads, and Windows platforms will be impacted.
2015 – Looking Back, Moving Forward
January 6, 2015 by
Bruce Morton
(Entrust)
Apple
Attack
CA/Browser Forum
CAA
Chrome
Code Signing
EV
Firefox
Forward Secrecy
Google
IETF
Malware
Microsoft
MITM
Mozilla
OpenSSL
PKI
Policy
RSA
SHA1
SSL 3.0
SSL/TLS
TLS 1.0
TLS 1.2
TLS 1.3
Vulnerability
Looking Back at 2014
End of 1024-Bit Security
In 2014, the SSL industry moved to issuing a minimum security of 2048-bit RSA certificates. Keys smaller than 2048 are no longer allowed in server certificates. In addition, Microsoft and Mozilla started to remove 1024-bit roots from their certificate stores. Hopefully, the key size change will support users through to 2030.
Extra Trips are for Frequent Flyers, Not SSL/TLS Performance
October 30, 2014 by
Wayne Thayer
Firefox
Forward Secrecy
Google
HSTS
OCSP
Revocation
RSA
SSL/TLS
TLS is quickly becoming a de facto requirement for every website due to increased concerns about spying and Google’s recent move to use HTTPS as a factor in search engine ranking. In a recent article we explained how HSTS helps website operators to ensure that their site is always using TLS, but now we want to ensure that your performance isn’t sacrificed in the name of enhanced security. While the myth that TLS slows down a website has been debunked, some basic settings can make a site using TLS even faster.
Perfect Forward Secrecy
April 11, 2014 by
Bruce Morton
(Entrust),
Rick Andrews
3DES
DH
ECC
ECDH
Forward Secrecy
OpenSSL
RC4
RSA
SSL/TLS
TLS 1.2
Recent revelations from Edward Snowden about pervasive government surveillance have led to many questions about the safety of communications using the SSL/TLS protocol. Such communications are generally safe from eavesdroppers, as long as certain precautions are observed. For example, configuring your web server to avoid using SSL2 and SSL3, favoring newer versions of TLS like TLS 1.2, selecting strong ciphersuites, etc.
But even if your server is configured properly, you still must secure the private key associated with your SSL certificate. In nearly all cases, the web site owner generates their key pair and sends only the public key to their Certification Authority (CA). The CA (and any eavesdropper) sees only the public key, and the private key cannot be derived from that. So the CA cannot reveal a web site owner’s private key to the government or an attacker, even if coerced to do so.
Reducing the Impact of Government Spying
April 4, 2014 by
Jeremy Rowley
CASC
Encryption
Forward Secrecy
Malware
PKI
RC4
RSA
SHA2
SSL/TLS
TLS 1.1
Vulnerability
Last year, Edward Snowden, an American computer-specialist working as a contractor for the National Security Agency (“NSA”), shocked web-users around the world by publicizing documents showing that the NSA was gathering intelligence on Internet users. The realization that the US government was gathering sensitive information has led to a worldwide demand for better protection of online communication and data and a general worry about the effectiveness of existing infrastructures. Specifically, some entities have asked whether PKI is still a robust way to protect online information.










































































